Crypto investors have long been targeted by attackers, who use various methods to drain their wallets. Today, the accounts of a popular Turkish trader were compromised within minutes. What’s more, this was done without clicking on any links or infecting their devices with viruses. So how does this happen? And what can be done to prevent it?
Crypto Wallets Hacked
A user named Coinmühendisi, known for their recent AVAX long position that earned them nearly $1 million in profits, became a target of attackers. They closed their position with significant gains during the recent price surge, but it wasn’t long before they fell victim to hackers. They posted the following on their social media account 50 minutes ago:
“My Türk Telekom SIM card has been stolen, and all my funds on exchanges are being withdrawn. I’m not receiving any calls on my phone, and all my emails have been stolen and passwords changed. They have withdrawn all my money from exchanges, and I’m in a very difficult situation. Please help. I’ve lost all my money, please help me. Someone authorized changed my SIM card, and everything is gone. My emails have changed, and I’m not even able to check my inbox. I don’t understand how they can change my SIM card.”
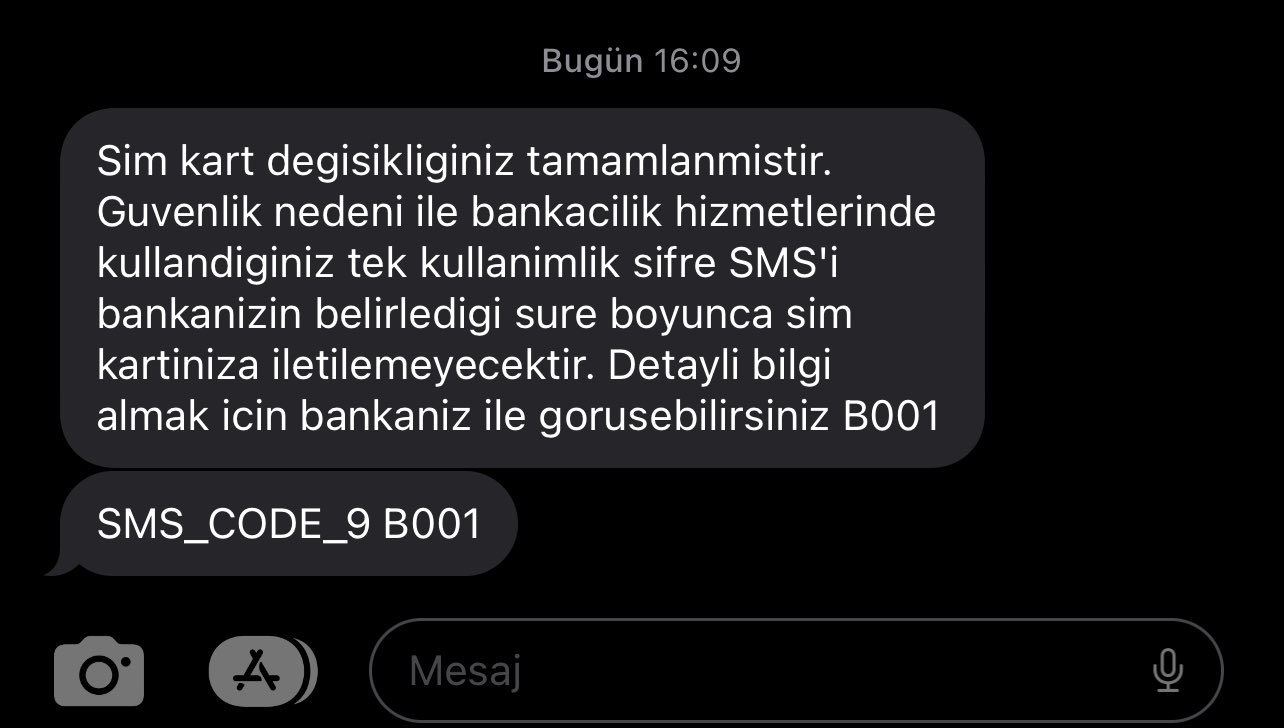
Yes, attackers copied the SIM card, reset the emails, and changed the exchange passwords. Then they started emptying the wallets. Moreover, once your SIM card is copied, it is not possible to prevent your account from being emptied. The user named Coinmühendisi realized that their card had been copied when they received an SMS notification.
How to Protect Yourself
First of all, it is not legally possible to obtain a SIM card without your personal application at the authorized dealer. Those who copy the card need to persuade a dealer to cooperate or hack their system. As a crypto investor, the first thing you can do is to be prepared for such attacks. When you encounter a SIM card issue on your phone, your number might have been transferred to a different device.
When your card is copied, you will receive an SMS message like the one above. You should quickly take action, contact the customer services of the exchanges, and remove the phone number associated with your email addresses. Attackers reset your email passwords first if you use the same phone number as the reset option. Additionally, if you have 2FA authentication, it will become useless once your Gmail account is compromised.
- You can acquire a separate number that you don’t share with anyone for use in exchanges. However, this is not a definitive solution as attackers can identify lines registered under your name using your national identification number illegally.
- You can use a different email address for 2FA authentication. Using a different number for this email address can enhance your security. You can even consider obtaining numbers from countries like Bulgaria or Ukraine and use them for the reset option. While attackers may be able to identify lines registered in your country, they may not be able to do the same for international lines.
- Disabling phone recovery option for your email addresses can also be a good solution. At this point, creating a strong password and designating a second email for recovery purposes can protect you from SIM card attacks.
- Creating a separate email address for each exchange will make it more difficult for attackers. Make sure to create complex passwords for your email addresses, just like your passwords, e.g., [email protected].
- Using Google Authenticator and Authy enhances security, but acquiring a YubiKey can further elevate your security.
- Keeping minimal balances on exchanges may be the best solution. If you can ensure their security, DeFi wallets are more difficult to hack compared to exchanges.
In addition to all of these, connecting to external networks with the devices you use to access your exchange accounts is risky, even if your SIM card is not copied. Attackers can intercept your traffic and gain access to your passwords. Always maintain a skeptical and cautious approach.