It remains difficult to fathom how protocols serving massive user bases continue to fall victim to such elaborate traps. The recent hack of Drift Protocol is only the latest episode in a long string of cyberattacks—often orchestrated by groups like North Korea’s infamous Lazarus and its offshoots—in which billions in digital assets have been stolen. This most recent breach left investors reeling and raised fresh concerns about security vulnerabilities plaguing even leading projects.
How attackers breached Drift Protocol’s defenses
The attack, which unfolded on April 1, initially appeared to some as an April Fool’s prank, but the Drift team’s somber announcement quickly dispelled any doubts. Despite using multisignature wallets as a requirement and fundamental security measure, attackers methodically gathered the necessary number of signatures to empty protocol-controlled wallets. In response, all protocol functions have been frozen and compromised wallets were removed from the multisig system. Cybersecurity firm Mandiant has launched an investigation into the incident.
Attackers established trust through in-person engagement
Intriguingly, the foundation for the breach was laid months in advance, with perpetrators—believed to be North Korean—initiating contact at a major crypto conference in fall 2025. Posing as representatives of a trading firm, they expressed interest in collaboration. Over the following six months, these individuals repeatedly met Drift staff face-to-face at various industry conferences across different countries. Such persistent and personal engagement brought an air of legitimacy to their presence and deepened the level of trust.
Previously, attackers employed social media or AI-powered video calls for social engineering. Increasingly, they are now capable of in-person engagement and, alarmingly, possess credible backgrounds in the tech sector. Verified professional histories made it even harder for teams like Drift to detect the ruse.
Following the initial connection, attackers organized group chats via Telegram and held extensive talks on trading strategies and potential vault integrations over several months. According to Drift’s latest report,
“Between December 2025 and January 2026, the group integrated into an ecosystem vault within Drift, which required submitting forms containing strategic details. Through numerous work sessions, they engaged with contributors, asked highly detailed and knowledgeable technical questions, and invested more than $1 million of their own capital. They deliberately and patiently built an operational footprint within the Drift ecosystem.
Integration discussions continued through February and March 2026. Drift participants met members of the group face-to-face at a number of major industry events. At this point, the relationship had persisted for almost half a year. These were not strangers; they were people Drift participants had worked with and met in person.”
The turning point: exploiting technical trust
Throughout the process, attackers routinely shared files, links, and purported project resources with the team. While the exact point at which a private key was compromised is unclear, the volume of file transfers and shared links made infiltration easier. In cybersecurity, terms like FUD (Fully Undetectable) and ‘binder’ refer to methods of cloaking malicious files. FUD encrypts a virus so antivirus programs are temporarily blind to it—often for two weeks to a month unless uploaded to online scanners, which may shorten that window. Using binder tools, the malware is then disguised as a PDF, PNG, or JPEG; opening what appears to be a harmless document activates the virus behind the scenes. There are yet more advanced techniques for formats like Word or Excel. These methods are so commonplace that even average hackers can execute them, underscoring the importance of heightened vigilance; similar attacks often go unreported in scenarios involving individual investors.
File-based malware was just one possible attack vector, granting complete control over affected devices. There are multiple ways to steal private keys, and the Drift team suspects one of three potential vectors was exploited:
- A team member may have cloned a malicious code repository shared under the pretense of “frontend deployment” for a vault.
- Another staffer might have been convinced to download a TestFlight application presented by the group as their own wallet product.
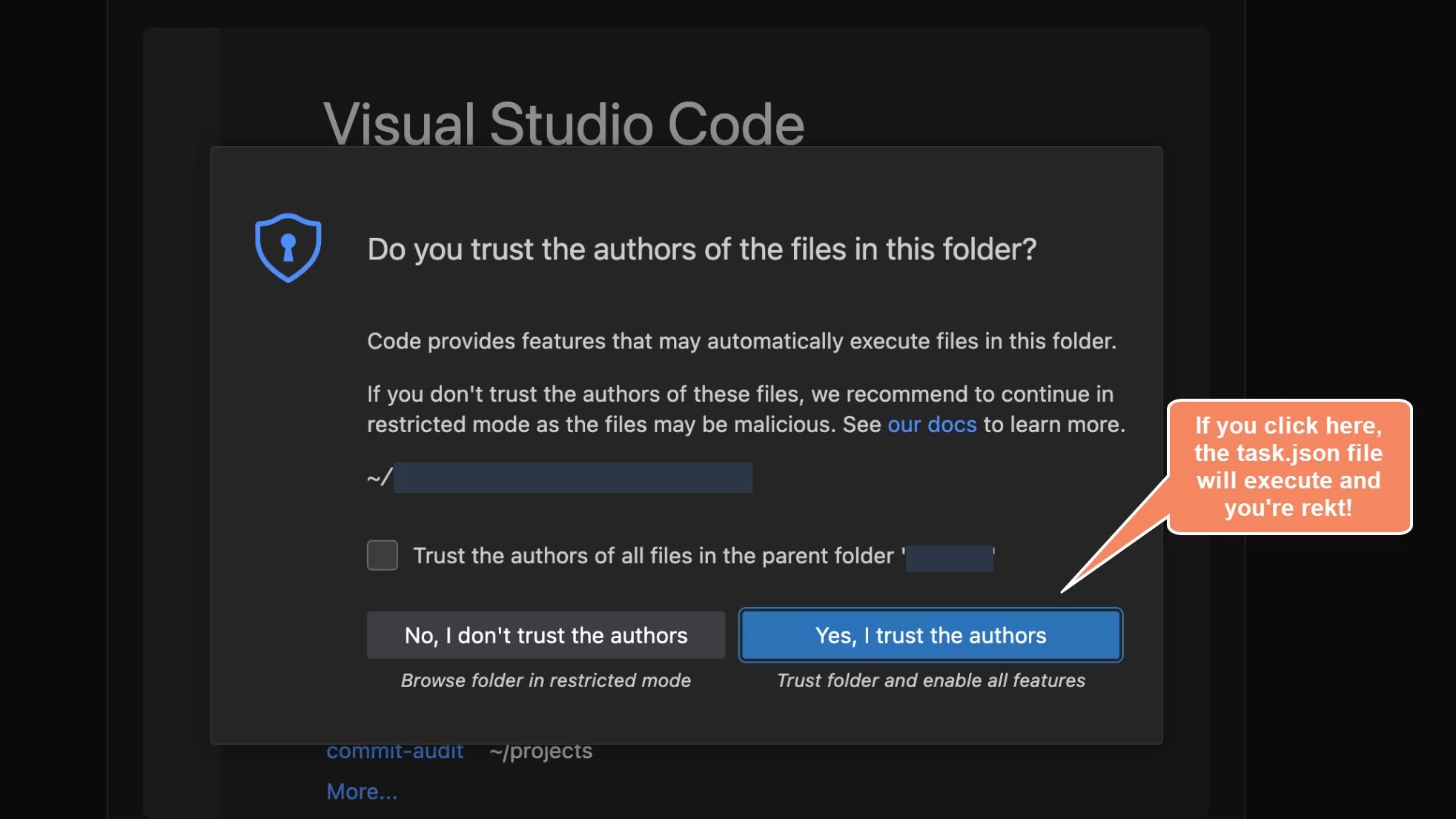
- A repository-based attack stemming from a known VSCode and Cursor editor vulnerability, which remained unpatched from December 2025 through February 2026. Opening a file or repo would silently execute arbitrary code without any warning or prompt, as flagged by security researchers at the time.
Such attacks can even leverage zero-day exploits, making detection nearly impossible. Indeed, the Drift team only discovered the breach once their protocol had already been siphoned of funds—days or even weeks after the initial compromise.
So, who was behind the operation? According to the incident report:
“Based on investigations by the SEALS 911 team and with moderate to high confidence, it is believed that the operation was carried out by the same threat actors identified by Mandiant as responsible for the October 2024 Radiant Capital attack, tracked as UNC4736. UNC4736 (also known as AppleJeus or Citrine Sleet) is affiliated with the North Korean state.
This attribution is supported both by on-chain evidence—funding trails tied to the Radiant attackers—and operational patterns, as the personas involved correlate with other known North Korea-linked activities.
It’s important to note that those present at in-person meetings were not North Korean nationals. Instead, it is well established that North Korean threat actors of this caliber use third-party intermediaries to facilitate face-to-face interactions.
Mandiant has not yet formally attributed the Drift breach to any group. Final attribution will depend on ongoing forensic analysis of affected devices.”
The Drift team’s use of isolated devices for communications possibly prevented greater loss; had malicious files been opened on core servers, the full extent of the protocol’s $285 million in assets might have been stolen. The fact that some team members were unaware they had been compromised raises uncomfortable questions about the overall operational standards within crypto startups. This stark lesson reinforces the necessity for regular security audits, penetration tests, and a healthy dose of skepticism in every collaboration.
Ultimately, the threat is not limited to major protocols; even ordinary investors could be targeted next. In the uncertain terrain of cryptocurrency, one must always choose between caution and exposure—often, only those who prioritize robust safeguards will avoid becoming the next headline.










