Mixin Network, an inter-chain asset transfer protocol, was hit by a $200 million hack attack on September 23rd. The team sent a message to the hacker behind the attack, offering a $20 million reward if the stolen assets were returned. The reason behind the hack is still unknown, but inter-chain protocols in the DeFi space continue to be targeted by major attacks.
The Team’s Last Resort
Mixin Network officials encrypted the message in a way that the hacker could understand and requested the return of the funds, emphasizing that the majority of the stolen assets belonged to users:
“Most of our platform’s assets belong to users, and we hope you can return them. You can keep 20 million dollars of the assets as a BUG Bounty reward.”
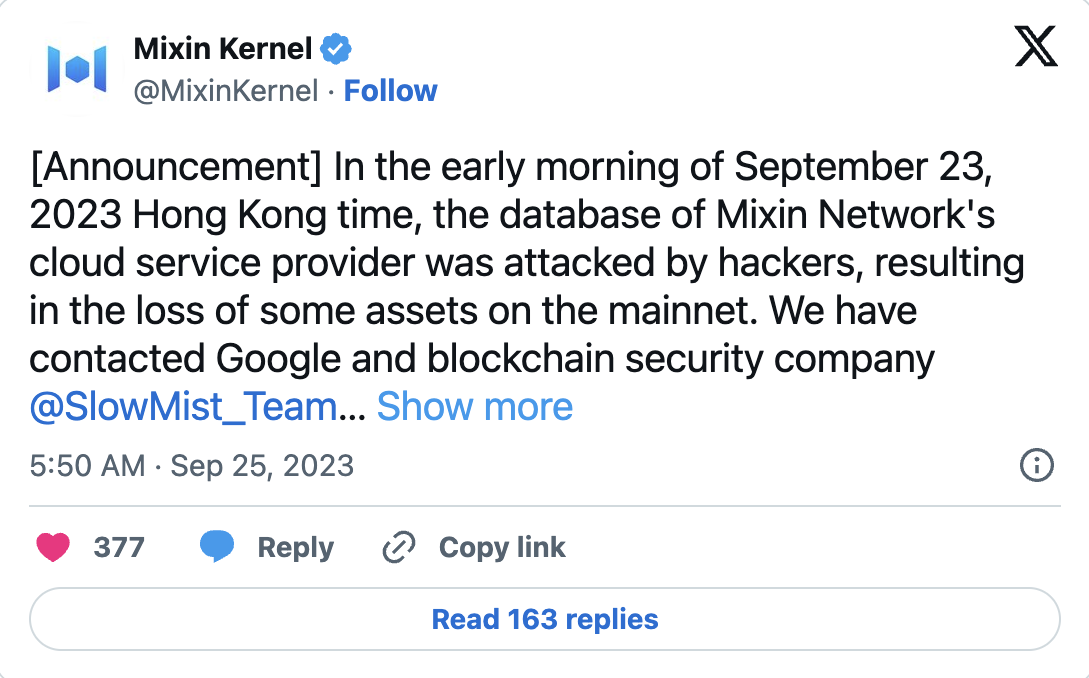
Mixin Network officials confirmed the attack on September 25th, stating that the attackers had successfully breached a third-party cloud service provider, resulting in the theft of approximately $200 million in assets.
Feng Xiaodong, the founder of Mixin Network, had previously announced how the damage would be compensated after the attack. According to Xiaodong, users would be immediately reimbursed up to 50% of the lost funds, and the remaining amount would be compensated with bond tokens tied to the protocol’s earnings.
Mixin Network officials have not yet disclosed the source of the vulnerability. However, an on-chain data analysis firm highlighted the hacker’s interactions with Mixin Network. According to the platform, the address associated with the hacker had received 5 Ethereum from Mixin in 2022.
DeFi Sector Suffers Major Losses from Attacks
It is still unclear how the attacker managed to steal $200 million worth of crypto assets through a data breach. Inter-chain protocols in the DeFi space continue to be targeted by the largest attacks in crypto history. A research study confirmed that over half of all DeFi attacks have targeted inter-chain protocols, resulting in losses exceeding $2.5 billion.

Cross-chain protocols are used to facilitate faster and easier transfers of crypto assets between different chains. As a result, platforms must hold significant assets in each ecosystem they serve. However, this situation weakens security measures to a significant extent, leaving protocols vulnerable to attacks.











